Key Takeaways
- Comprehensive risk assessment is the foundation of effective event security, helping identify potential threats before they materialize
- The ideal security staff-to-attendee ratio ranges from 1:50 to 1:100, depending on your event type and risk level
- Multi-layered access control systems combining technology and human verification create the most secure entry points
- Clear communication protocols between security team members can reduce incident response time by up to 60%
- Post-event security reviews are essential for continuous improvement, with 87% of successful event planners conducting thorough debriefings
- New England Security’s guards are fully certified as Crowd Managers, ensuring they are trained to effectively oversee and maintain safety during events and large gatherings.
The difference between a successful event and a disaster often comes down to how well you’ve planned for security. In today’s world, event security isn’t just about checking bags at the door—it’s a comprehensive system that protects attendees, staff, and your organization’s reputation. Professional security management from Belfry Software can transform your approach to event safety, integrating modern technology with proven security protocols. Whether you’re organizing a corporate conference, music festival, or community gathering, the safety of your attendees should always be your top priority.
Event security has evolved dramatically over the past decade, responding to new challenges and leveraging new technologies. With the right approach, you can create a secure environment without compromising the attendee experience. Let’s dive into the essential components of effective event security management.
Why Event Security Matters More Than Ever Today
The landscape of event security has transformed significantly. Today’s events face a wider variety of potential threats than ever before, from digital security breaches to more traditional concerns like overcrowding and medical emergencies. Recent studies show that 78% of attendees consider security measures when deciding whether to attend an event, making security not just a safety concern but a business imperative.
High-profile incidents at events worldwide have heightened awareness and expectations among attendees, sponsors, and insurers. The financial implications of inadequate security can be severe—beyond the immediate human impact, the average liability claim from a security incident exceeds $300,000, and that doesn’t include the incalculable damage to your brand’s reputation.
Furthermore, regulatory requirements are becoming increasingly stringent. Many venues and local authorities now require detailed security plans before granting permits for events. Failure to comply with these requirements can result in last-minute cancellations or significant fines. The days of treating security as an afterthought are long gone.
Creating Your Complete Event Security Plan
A comprehensive security plan serves as the backbone of your event’s safety strategy. This document should be developed months before your event, allowing adequate time for review, refinement, and coordination with all stakeholders. The most effective security plans are living documents that evolve as new information becomes available or circumstances change.
Assessing Venue Vulnerabilities and Threat Levels
Every venue has unique security challenges that must be identified well in advance. Begin with a thorough walk-through of the space, ideally accompanied by venue staff and security professionals. Look for potential access vulnerabilities, bottlenecks that could create dangerous crowding, and areas with limited visibility. Consider factors like multiple entry points, proximity to high-traffic areas, and existing security infrastructure.
Your threat assessment should evaluate both the likelihood and potential impact of various scenarios. Consider the profile of your event, the nature of attendees, historical incidents at similar gatherings, and current threat intelligence. Rate each potential threat on a scale from low to critical, allowing you to prioritize your security resources accordingly.
“The most dangerous security threats are often the ones you haven’t considered. A systematic risk assessment process reduces these blind spots by forcing planners to think beyond obvious concerns.” — Event Security Association
Defining Clear Security Objectives
Effective security planning requires specific, measurable objectives rather than vague goals. Instead of simply aiming to “have good security,” establish concrete targets like “screen 100% of attendees within an average wait time of less than 5 minutes” or “maintain continuous surveillance coverage of all access points.” These specific objectives help guide resource allocation and provide clear metrics for evaluating performance.
Your security objectives should balance protection with practicality. Excessively intrusive security measures can negatively impact the attendee experience, potentially harming attendance at future events. The best security plans find the sweet spot where robust protection coexists with a positive, welcoming atmosphere.
Setting Up Security Zones and Access Points
Dividing your venue into distinct security zones with varying access requirements is a fundamental security strategy. This layered approach allows you to concentrate resources where they’re most needed while maintaining appropriate security levels throughout the venue. Typically, venues should be divided into public areas, general attendee areas, backstage/operations zones, and high-security areas like cash handling locations or VIP spaces.
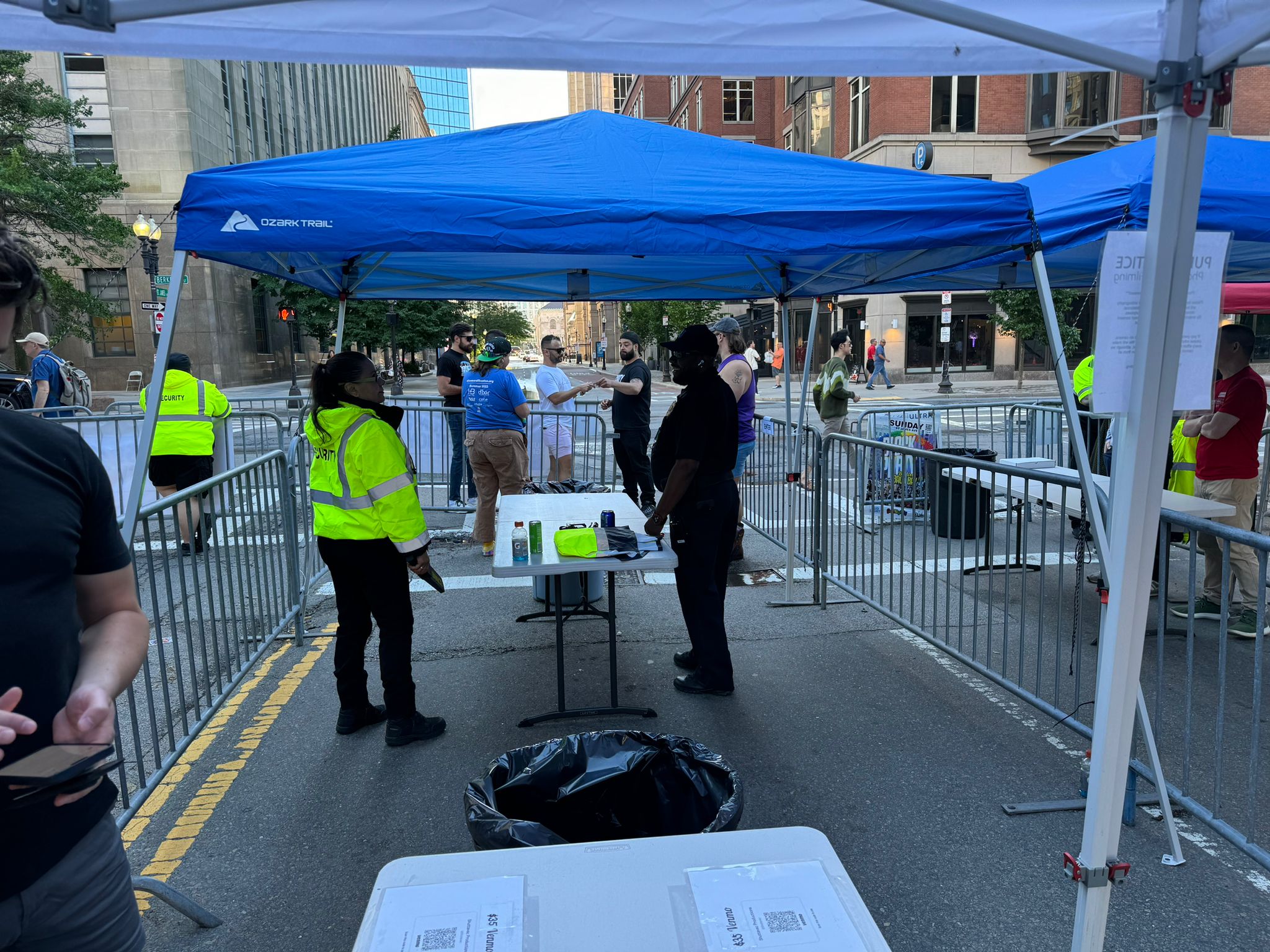
Each zone boundary requires carefully designed access control systems. Consider how attendees will flow through your venue, identifying natural bottlenecks where access checking can occur without creating dangerous crowding. The most effective setups include staging areas where attendees can prepare for security screening, clear signage explaining procedures, and sufficient staffing to maintain efficient processing even during peak arrival times.
- Outer perimeter: General security presence, initial crowd management
- Entry points: ID verification, ticket scanning, prohibited item screening
- Internal checkpoints: Credential verification for restricted areas
- Emergency exit planning: Ensuring quick evacuation without compromising security
- Command center: Centralized monitoring and coordination hub
Coordinating With Local Law Enforcement
Establishing strong relationships with local law enforcement and emergency services is a critical yet often overlooked component of event security. Make initial contact at least 3-4 months before your event, providing clear information about the nature, scale, and specific security concerns of your gathering. Most police departments have dedicated units or officers who specialize in event security and can provide invaluable guidance tailored to your local area.
Beyond simply notifying authorities about your event, consider how they’ll integrate with your security operations if needed. Establish clear protocols for when and how to involve law enforcement, create dedicated communication channels, and potentially arrange for on-site presence depending on your event’s profile. Many departments offer paid detail officers who can provide an official security presence while being familiar with your specific event plans.
4. Communication Equipment for Fast Response
- Two-way radios with dedicated security channels
- Mobile phone backup systems with pre-programmed contacts
- Earpieces for discrete communication
- Emergency notification systems for mass alerts
- Central command post with monitoring capabilities
Effective communication forms the backbone of any security operation. Your security team needs reliable, instant communication capabilities that function regardless of cellular network congestion or power outages. Two-way radios remain the gold standard for event security, offering dependable performance when smartphone networks become overwhelmed during large gatherings.
Establish clear communication protocols before the event begins. Each team member should understand exactly how to report incidents, request backup, or signal an emergency. Using standardized codes for different situations (like “Code Blue” for medical emergencies) allows for quick, clear communication without alarming nearby attendees unnecessarily.
The command center should serve as your communication hub, equipped with monitoring systems for surveillance feeds, staff locations, and incident tracking. This central nerve center needs redundant communication systems and should be staffed by experienced personnel capable of coordinating multiple security elements simultaneously.
Remember that communication extends beyond your security team. Develop protocols for how security will communicate with event staff, vendors, performers, and if necessary, attendees during emergencies. Pre-scripted announcements for common scenarios can prevent panic and facilitate orderly responses to incidents.
5. Clear Emergency Exit Planning
Every minute counts during an evacuation, and poorly planned exit routes can quickly turn dangerous. Work with your venue to identify, mark, and maintain all emergency exits, ensuring they remain unobstructed throughout your event. Your security plan should include specific staff assignments for guiding attendees to exits during emergencies and verifying that all areas have been evacuated.
Conduct a timed evacuation drill with your security team before the event opens. This practice run helps identify potential bottlenecks or confusion points in your evacuation plan. Pay special attention to accommodations for attendees with disabilities, ensuring accessible evacuation routes are clearly marked and staffed with trained personnel who can provide assistance.
6. First Aid Stations and Medical Preparedness
Medical emergencies can happen at any event, regardless of size or type. Establish clearly marked first aid stations staffed by qualified medical personnel, with appropriate supplies for treating common injuries and conditions. For larger events, consider having dedicated emergency response teams with advanced medical training who can quickly reach incidents anywhere in your venue. Your medical plan should include protocols for summoning external emergency services, designated ambulance access points, and procedures for transferring patients to local hospitals.
7. Crowd Management Techniques
Effective crowd management prevents dangerous situations before they develop. Train your security staff to recognize early warning signs of crowd issues, such as unusual density, aggressive behavior patterns, or sudden movements. Implementing capacity controls for different venue areas helps prevent dangerous overcrowding, while physical barriers and clear signage can naturally guide attendee flow without creating friction.
For high-energy events like concerts, implement specific crowd safety measures like barriers to prevent crushing near stages. Audience spotters positioned on elevated platforms can monitor crowd conditions and alert security to developing problems. Remember that crowd management isn’t just about control—it’s about creating an environment where attendees naturally behave in safe, orderly ways through thoughtful venue design and positive security engagement.
Technology That Makes Your Event Safer
Today’s event security benefits from remarkable technological advances that enhance capabilities while reducing costs. From AI-powered surveillance to digital credentials, strategic technology deployment can dramatically improve your security posture. The key is selecting solutions that integrate seamlessly with your overall security plan rather than treating technology as a standalone solution.
CCTV and Surveillance Options
Modern surveillance systems extend far beyond basic cameras. Today’s options include high-definition video with low-light capabilities, thermal imaging for perimeter monitoring, and AI-powered analytics that can automatically detect unusual behavior patterns or prohibited items. For temporary installations, consider rapidly deployable systems using wireless connectivity and battery power, eliminating the need for extensive infrastructure modifications.
When designing your surveillance coverage, prioritize high-risk areas like entry points, crowded spaces, and cash handling locations. Ensure your command center has appropriate monitoring capabilities and recording systems that comply with data retention regulations. Remember that visible surveillance also serves as a deterrent—strategic placement of obvious cameras can discourage problematic behavior.
Digital Access Control Solutions
Digital ticketing systems with QR codes, RFID wristbands, or NFC technology provide powerful tools for managing venue access. These systems prevent counterfeiting, enable rapid entry processing, and create digital records of all venue entries. Advanced options can include biometric verification for high-security areas, real-time occupancy tracking for capacity management, and integration with access control systems to flag persons of concern.
Emergency Notification Systems
Mass notification capabilities are essential for communicating with attendees during emergencies. Modern systems can deliver alerts through multiple channels simultaneously, including venue screens, speaker systems, mobile apps, text messages, and even temporarily overriding Wi-Fi networks with emergency information. Your notification plan should include pre-scripted messages for common scenarios, clear authority guidelines for who can issue alerts, and testing procedures to ensure system functionality.
Special Security Considerations for Different Event Types
Security needs vary dramatically depending on your event type. A corporate conference requires different measures than a music festival, and a high-profile political gathering presents unique challenges compared to a community fair. Understanding these differences allows you to allocate security resources efficiently while addressing the specific risks associated with your event profile.
The demographic composition of your attendees significantly impacts security planning. Events attracting younger crowds may face different challenges than those primarily attended by families or business professionals. Historical data from similar events provides valuable insights into likely security concerns, allowing for more precise preparation.
Your venue location also influences security requirements. Urban settings present different challenges than rural locations, with considerations ranging from transportation security to coordination with neighboring properties. Environmental factors like weather patterns should factor into contingency planning, particularly for outdoor events where rapid evacuation might become necessary.
- Public profile: Higher-profile events attract more security attention
- Alcohol service: Increases likelihood of behavioral incidents
- Duration: Multi-day events require security shift planning and heightened vigilance
- Ticket price point: May influence attendee expectations and behavior
- Special attendees: VIPs or controversial figures require additional security layers
Large Outdoor Festivals
Outdoor festivals present unique security challenges due to their scale, perimeter control difficulties, and weather vulnerabilities. Establish a clear perimeter using a combination of natural barriers, temporary fencing, and strategic security positioning. Consider using drone technology for aerial monitoring of crowd patterns and perimeter integrity, particularly for events covering extensive grounds.
Weather monitoring becomes a critical security function for outdoor events. Establish clear thresholds for weather-related actions, from simple announcements to full evacuations. Your weather plan should include designated shelters, communication procedures, and staff responsibilities during weather emergencies.
Camping areas require specialized security considerations, including overnight patrols, fire safety measures, and clear boundaries between camping zones and performance areas. Implement designated pathways between camping and main event areas with appropriate lighting and security presence to ensure attendee safety during nighttime movement.
Corporate Conferences
Corporate events typically prioritize unobtrusive security that maintains a professional atmosphere while addressing specific risks like intellectual property protection, executive safety, and corporate espionage concerns. Implement discrete access control systems using professional credentials that integrate with name badges, avoiding security measures that create a fortress-like atmosphere.
Data security becomes a significant consideration for corporate gatherings. Ensure your security plan addresses Wi-Fi network protection, secure areas for sensitive discussions, and protocols for protecting confidential materials. Consider implementing temporary secure rooms for highly sensitive meetings using soundproofing, electronic countermeasures, and enhanced access controls.
- Credential management systems with photo verification
- Executive protection for high-profile attendees
- Intellectual property protection protocols
- Secure storage for sensitive materials
- Background checks for staff with access to restricted areas
For international corporate events, be aware of varying security expectations and requirements across different cultures. Some international attendees may expect higher security levels or have specific concerns based on their countries of origin. Working with a security consultant familiar with international business security can help navigate these complexities.
Celebrity Appearances and VIP Protection
Events featuring celebrities or VIPs require specialized security approaches that balance protection with accessibility. Conduct advance planning with the VIP’s security team to align protocols and responsibilities, ensuring seamless coordination during the event. Remember that VIP security extends beyond the individual to include secure transportation, private areas, and protection from excessive fan attention.
“The most effective VIP security is invisible to the public but omnipresent to those who are looking for vulnerabilities. It creates a protective bubble without building walls that detract from the experience.” — Former Secret Service Agent Robert Johnson
Establish clear procedures for managing fan interactions, including photo opportunities, autograph sessions, and chance encounters. These high-demand moments create potential security vulnerabilities and require careful planning. Consider using timed tickets for meet-and-greets, physical barriers to maintain orderly queues, and security personnel specifically assigned to monitor these interactions.
Media management becomes a critical security function when celebrities are involved. Create designated media areas with appropriate credentialing systems, and establish clear guidelines for photography and interviews. Unauthorized media can create security disruptions, so train your team to recognize and address improper media behavior promptly.
Sports Events
Sporting events combine passionate fans, team rivalries, and often alcohol service—creating unique security challenges. Implement section-based security staffing where personnel are assigned to specific areas rather than roving, allowing them to recognize regular attendees and spot unusual behavior. Pay special attention to rivalry games where tensions may run higher, potentially increasing security staffing and implementing additional screening measures for known trouble spots.
How to Handle Security Incidents When They Happen
Despite the most thorough planning, security incidents can still occur. Your response in these moments often determines whether a minor issue remains contained or escalates into a major incident. Develop detailed response protocols for common scenarios, from medical emergencies to disruptive behavior to serious security threats. Each protocol should clearly define staff responsibilities, communication procedures, documentation requirements, and follow-up actions.
Creating an Incident Response Plan
An incident response plan serves as your roadmap during security emergencies, providing clear guidance when stress levels are high and decisions must be made quickly. The most effective plans use a modular approach, with specific protocols for different incident types that can be combined as needed for complex situations. Start by identifying the most likely security scenarios for your event type, then develop detailed response procedures for each.
Your incident response plan must clearly define roles and authority during emergencies. Establish a clear chain of command, decision-making thresholds for different response levels, and explicit procedures for escalating incidents when necessary. This clarity prevents confusion during critical moments when hesitation could worsen an incident.
“In a security incident, every second of indecision compounds the problem. Well-trained staff working from clear, practiced protocols can resolve many situations before they escalate to crisis level.” — Event Security Institute
Regular rehearsal of response protocols is essential. Conduct tabletop exercises where your security leadership walks through various scenarios, identifying potential gaps or confusion points in your plans. For high-risk events, consider full-scale drills involving your entire security team, using role players to simulate challenging situations.
De-escalation Techniques
The most successful security teams excel at de-escalating situations before they become serious incidents. Train your staff in proven de-escalation techniques, including maintaining appropriate distance, using calm tones, avoiding confrontational stances, and employing active listening. The goal is to resolve situations with minimal force while maintaining safety for all parties. Remember that visible security response can sometimes escalate tensions, so train staff to assess whether a low-profile approach might be more effective initially.
Medical Emergency Protocols
Medical emergencies require particularly swift, coordinated responses. Your medical response plan should include clear procedures for incident assessment, triage protocols for multiple casualties, and seamless handoff to external emergency services when needed. Ensure all security staff know the location of medical equipment like AEDs, first aid kits, and emergency medications.
Consider implementing a color-coded system for medical emergency severity, allowing for appropriate resource allocation. Train security personnel in basic first aid and CPR, enabling them to provide initial assistance before medical professionals arrive. This bridging capability can be critical in life-threatening situations where minutes matter.
Weather Emergency Procedures
Weather emergencies require rapid decision-making and clear communication chains. Establish specific weather monitoring responsibilities, defining exactly who tracks forecasts and who has authority to initiate weather-related actions. Your plan should include graduated response levels—from simple announcements to full evacuation—with clear triggers for each level.
For outdoor events, lightning presents a particular danger requiring specific protocols. The standard approach is the “30-30 rule”: suspend activities when lightning is within 30 seconds (6 miles) of your location, and resume only after 30 minutes have passed since the last lightning strike within that radius. Ensure you have designated lightning shelters that meet safety standards, avoiding open structures, isolated trees, or metal objects. For additional safety measures, consider expert tips for perimeter security during events.
After the Event: Security Review Process
The post-event security review is where valuable lessons are captured and improvements identified. Schedule this review within 48-72 hours of event conclusion, while details remain fresh in everyone’s memory. Include representatives from all security functions, venue management, and key event staff to ensure comprehensive perspectives.
Structure your review to examine both what went well and what needs improvement. The most productive security reviews maintain a solutions-focused approach rather than assigning blame, encouraging honest assessments of performance gaps. Document specific action items with clear ownership and timelines for implementation in future events. For more insights, consider these recommendations from physical security assessments.
Debriefing Your Security Team
Conduct thorough debriefings with your security personnel, using a structured format that captures specific observations and recommendations. The front-line security staff often notices issues that management might miss, from inefficient procedures to potential vulnerabilities. Create an environment where staff feels comfortable providing honest feedback, potentially including anonymous submission options for sensitive observations.
Documenting Incidents and Near-Misses
Comprehensive incident documentation serves multiple purposes, from improving future planning to protecting against potential liability. Develop standardized incident reporting forms that capture essential details like time, location, individuals involved, actions taken, and resolution. Include space for security staff to note contributing factors and preventive recommendations.
Pay particular attention to “near-miss” incidents—situations that could have become serious problems but were successfully prevented or contained. These near-misses often provide valuable insights into vulnerable areas of your security plan without the negative consequences of actual incidents.
Create a searchable incident database that allows you to identify patterns across multiple events. This longitudinal view helps identify recurring issues that might not be apparent when examining single incidents in isolation. Categorize incidents by type, severity, location, and resolution method to facilitate meaningful analysis. For more insights on enhancing safety, consider mobile patrol services as part of your security strategy.
- Date, time, and exact location of incident
- Personnel involved (both security and civilians)
- Detailed incident description and timeline
- Actions taken and their effectiveness
- Any injuries, property damage, or other consequences
- Contributing factors that enabled or exacerbated the incident
- Recommendations for future prevention
Preserve all security footage and communications related to significant incidents. These records provide invaluable context for understanding how situations developed and how effectively your team responded. Establish clear retention policies that comply with legal requirements while maintaining adequate records for internal review.
Applying Lessons to Future Events
The true value of your security review emerges when insights are systematically incorporated into future planning. Develop a formal process for translating lessons learned into specific security plan modifications, whether adjusting staffing levels, enhancing training, or implementing new technologies. The most effective organizations maintain a security knowledge base that grows with each event, creating institutional memory that persists even when individual staff members change.
Consider developing a security maturity model that helps track your organization’s progress in different security dimensions over time. This structured approach helps prioritize improvements and demonstrate security enhancements to stakeholders like insurers, venues, and sponsors. Remember that security planning is an evolutionary process—each event should be safer than the last as you incorporate new lessons and adapt to changing conditions.
Frequently Asked Questions
After consulting with hundreds of event planners and security professionals, certain questions consistently arise regarding event security management. These FAQs address the most common concerns and misconceptions about creating secure events without compromising the attendee experience.
While every event has unique security considerations, these answers provide foundational guidance that can be adapted to your specific circumstances. For complex security situations or high-risk events, consider consulting with a professional security advisor who can provide tailored recommendations.
What’s the biggest security mistake event planners make?
The most common mistake is treating security as a last-minute consideration rather than integrating it throughout the planning process. When security planning begins late, options become limited, costs increase, and compromises often result in vulnerability gaps. Security considerations should influence decisions from venue selection to scheduling to staffing levels, requiring early integration in the planning timeline.
Another frequent error is overreliance on technology without adequate human support. Even the most sophisticated security systems require trained personnel who understand how to interpret information and respond appropriately. The most effective security approaches combine technological tools with well-trained staff who exercise good judgment in dynamic situations.
How much of my event budget should go toward security?
Security budgets typically range from 2% to 15% of total event costs, varying significantly based on risk profile, attendee numbers, venue requirements, and event type. High-risk events like major concerts or political gatherings typically require higher security investments, while smaller, lower-profile events might need less extensive measures. Rather than using arbitrary percentages, conduct a thorough risk assessment and build your security budget based on the specific requirements identified in that process.
Do I need to tell attendees about security measures in advance?
Transparency about basic security measures generally improves the attendee experience. Providing advance information about entry procedures, prohibited items, and what to expect during security screening helps attendees prepare appropriately, reducing frustration and entry delays. This communication can be incorporated into ticket information, pre-event emails, and your event website.
However, certain security details should remain confidential. The specific positioning of security personnel, surveillance capabilities, and response protocols should not be publicly disclosed. The goal is to inform attendees about aspects that affect them directly while maintaining appropriate confidentiality about security operations.
Can I be held liable if something happens at my event?
Event organizers have a legal duty of care to take reasonable steps to ensure attendee safety. Failure to implement appropriate security measures could potentially result in liability claims if incidents occur that could have been reasonably prevented. Courts generally evaluate whether security planning met industry standards and whether organizers addressed foreseeable risks appropriately.
Documentation is your strongest protection against liability claims. Maintain detailed records of your risk assessment process, security planning decisions, staff training, incident response procedures, and any security incidents that occur. This documentation demonstrates your due diligence in addressing security concerns, even if unforeseen incidents occur despite your best efforts.
How do I balance tight security with a positive guest experience?
The key to balancing security with experience lies in thoughtful design and professional execution. Well-designed security measures incorporate efficient processes, clear communication, and courteous staff, minimizing friction for compliant attendees. Invest in training that emphasizes customer service skills alongside security protocols, helping staff maintain a welcoming demeanor while effectively enforcing necessary measures.
Consider using a layered security approach where more visible measures focus on customer service while less visible elements provide robust protection. For example, friendly greeters might conduct initial bag checks while more intensive screening happens less visibly. Technology can also help create this balance—for instance, using RFID wristbands for access control eliminates the need for repeated ID checks throughout an event.
When organizing a large event, ensuring the safety of all attendees is paramount. This involves meticulous planning and coordination with local authorities, as well as hiring a professional security team. One effective strategy is to choose the right security personnel to monitor the event, manage crowd control, and respond to any incidents swiftly. By implementing these measures, event organizers can create a secure environment that allows guests to enjoy the festivities without concern.